Today a device I forgot I ordered arrived, the Sonnet Labs One, a mesh point that reports to connect two places over lower frequency radio to allow large mesh networks. It works by getting one of the units and connecting it to your local wifi. Then the other one, according to the box can be up to 1ish miles in a city, and up to 10 miles out in the middle of no where. When I got it I unpacked it, and all that was in the box was the device, a micro USB cable, and a charger. Where are the instructions? I check the other (you need at least 2, or hope your town has some other people who got them years ago on Kickstarter or Indiegogo (yes they did both) ) and that also didn’t have instructions.

Box 





Ah the top of the box says sonnetlabs.com/start, perfect! 404 page not found, with a few other links, which also 404. Looking on the Indiegogo and Kickstart pages most people are still waiting for theirs, so I guess I am too early for the website? The sonnetlabs website also shows an early mockup of the device and nothing what it looks like now. I started digging through comments, and looking at their GitHub. I have pieced together some aspects of the device and figured I would start a manual since so far non exists. And at this point, the project seems to have maybe 1 or 2 people working to try to fulfill it. I would be happy to chat with the devs.
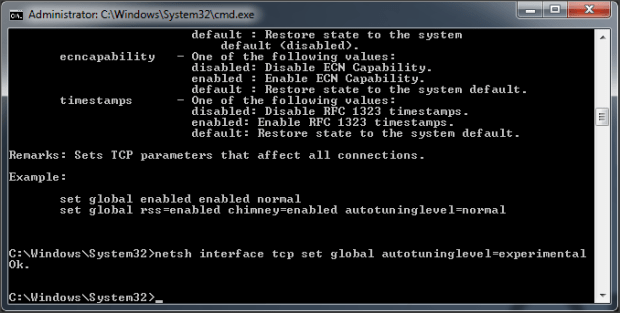
Turning on the device:
- The first flag contains a port for an antenna, the second has the micro USB charging port, and a micro SD card slot, the last has a USB host port to charge your devices.
- Plug in the included charger into the middle micro USB port
- Hold the Orange button for about 3 seconds and a green light should appear on the top of the unit
Connecting to the device, and to the internet:
- When the unit is on, you should see a new Wifi network near by, Sonnet-XXXX connect to this with the password of “sonneteer”
- Note: I had issues with my Mac doing this and had to manually enter the credentials
- The web server that hosts the app takes a minute to start, if you try to go to it too fast it will fail to load
- In a browser go to https://app.sonnetlabs.com, the IP is usually 192.168.47.1; but if you go to the IP the settings menu seemed total for me, it looks like they hard coded that URL in some locations
- There will be an error about the certificate, this is because the device made it, accept to continue, you may have to hit “Details” or “Advanced”
- You should see the login screen, click “Register New User”
- This makes a user to send messages, and use the basic aspects of the device, fun fact all this data is stored locally in your browser, so the users generally don’t matter. This does secure your chat message data, because you need to use that exact browser and that exact device to ever see these messages again. If you change the address you are going to, or the browser, or anything you need to go re-register a user.
- The Administrative password, set later, does actually store on the device and persist
- Put in a name, username, and password

- Once you see “Registration Successful” go back to the login screen and login
- Note: Hitting the “Enter” key on the password field doesn’t trigger a login, you need to click “login” (at least in Firefox)
- Now you are at the default page, “Contacts”, go to the “Settings Page”

- At the bottom of the “Settings” page it will say “Set New Password” and “New password”, you have to put something in here to get Admin access to the device, that isn’t clear, but it is needed. This is saved to the device.
- Note: This password is entered later in the UI and is just displayed on your screen, don’t make it something you don’t want people to see
- Once you set a password there, you will get a real “Admin” page
- Here you can click “Wifi” and start the process to connect to your own wifi network

- This took a minute, then mine displayed a green check mark and I could connect to the internet, through my internet, even though I was bouncing through the device
- Note at this time, I have gotten the two devices to use the “Chat” function, but not the mesh internet functions
Using Chat:
I was able to get chat to work between two of the devices, setting up one, then turning the other one seems to auto pair them. At this time I can not find any user interface on how to confirm/configure/see anything about the mesh. But Chat worked… so that’s something.
- Login to the web interface
- Go to “Contacts” on BOTH devices
- Click the + in the top right
- Select “From Network”

- If both sessions are online, you should see the other user
- Then if you can, you can click there name and this will send a request to add
- On the second device, there should be a red dot on the + in the top right of “Contacts” screen, go to the +
- Select “Requests” and approve the request

- Then you can chat, I haven’t done much testing on how much caching of messages the devices do, but in my first test one device missed a message because the window timed out and was “offline” again
- Note: If you see “Offline” as a bar at the top of the Window, your browser has disconnected from the device itself, clicking “Offline” should reconnect
I have not gotten QR codes to work, even with a very clear photo.
I took some screen shots of other screens. If you want more info, or have more info please leave a comment!
Additional Info:
I found a bunch of info poking around online, here are some notes:
Github for the app the device runs, but an OLD build: https://github.com/SonnetLabs/sonnet-webapp/
People talking about the device: https://community.gotennamesh.com/t/sonnet-devices-beta/4328/22
From what I can tell at the address above, a user states he was working with the devs and got SSH access to the device. I believe the image he had was a dev build with SSH installed, and the normal image we all have on the production units have this disabled.
The creators posted a early draft of a manual a while ago, copy below for archiving: https://www.dropbox.com/s/avmes7rhanx2vli/Sonnet%20User%20Manual%20v0.4.pdf
The FCC registered manual, very light: https://fccid.io/2AN8Z-SONNET/Users-Manual/user-manual-4003660
And the last laugh, there is a subdomain under sonnetlabs.com that the Digital Ocean server now belongs to someone else, so hilariously redirects. I give you lithium.sonnetlabs.com