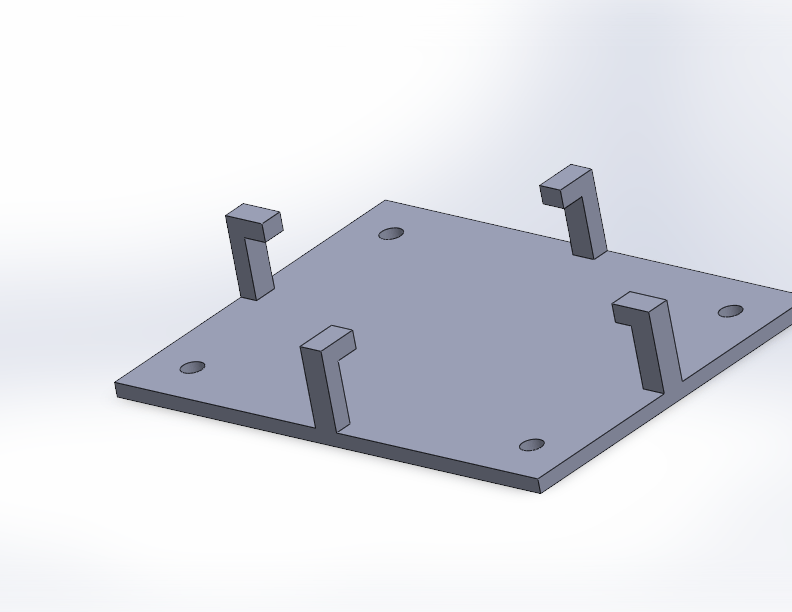
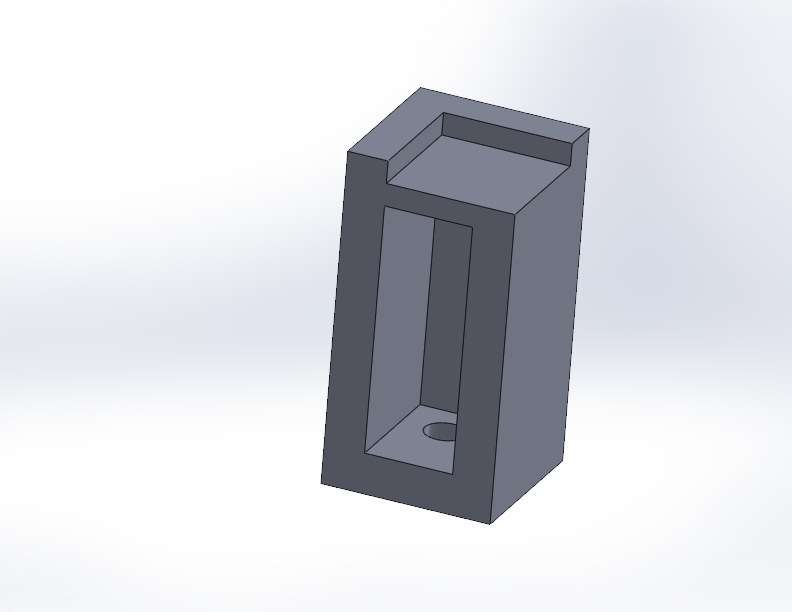
I use Solidworks Connected Makers edition to do a lot of my 3D Modeling. I had used Fusion 360 in the past, but they kept changing the license and what file types you could export, so I moved to Solidworks. As many posts from the community say, sometimes it’s like the company is trying to make you mad. Every year or so we get the next update, that you have to do because it’s a web-connected (for no reason) platform; and somehow the install breaks and won’t work. I spent a sometime trying to find all the different bits to delete to get it to install properly and wanted to document it. Once you get Solidworks in working order, it works well. It’s getting it there that is difficult.
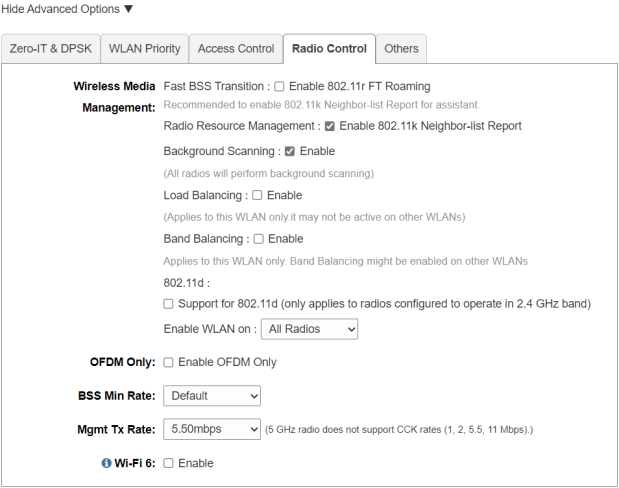
I had a failed install, the Solidworks site thought the application was installed, but when I clicked run, I got “failed to launch application, not found”. I uninstalled anything related to Solidworks or Dassault Systemes. Then I found and deleted the following.
Files:
- C:\Program Files\Dassault Systemes\SOLIDWORKS 3DEXPERIENCE
- %appdata%\SOLIDWORKS
- %appdata%\DassaultSystemes
- C:\ProgramData\DassaultSystemes
- C:\ProgramData\SOLIDWORKS
Registry:
- Go to HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData
- Search for “Solidworks”, I found items like
\S-1-5-18\Products\0911033B9E8C8E647ABE3D57D2083CB1\InstallProperties, where DisplayName was “Solidworks 2020”, delete anything related to Solidworks at the Products level.
- Search for “Solidworks”, I found items like
- Delete “HKEY_LOCAL_MACHINE\SOFTWARE\Dassault Systemes”
- Delete “HKEY_LOCAL_MACHINE\SOFTWARE\SolidWorks”
- Delete “HKEY_CURRENT_USER\SOFTWARE\Dassault Systemes”
- Delete “HKEY_CURRENT_USER\SOFTWARE\SolidWorks”
Even in the best conditions, on a fast machine it will take a LONG time to install, 3+ hours, looking like nothing is happening, I left it overnight. The x MB/y MB installed will not always progress for a while.
Logs in: C:\Program Files\Dassault Systemes\SOLIDWORKS 3DEXPERIENCE\InstallData\log
The install seems to install 4.5 billion MSI files, and then after each runs “.NET Optimization Service”; if your install is progressing, that service should periodically jump in CPU usage. My install halted at 76% 6122MB/14942MB installed for a long time; again, I left it overnight and it managed to finish.
I hope this helps someone. If others have issues or fixes, please leave a comment; maybe together we can get this program to work. In the end, mine worked after being left overnight, and now everything is functioning well with the 2025 release.
Update:
I went to reinstall and got the following errors:
Failed to get msi version for UpgradeCode [{B54313C8-7B46-297F-3AC1-85D9EFD5ECB7}].
Technical details:
The property is unrecognized
Error code: 1608
Invalid data in HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\BE85C2B02A76B522062B1D99E055DD33
Action CheckInstalledMsiVersionAction from feature CODE\win_b64\SWXDesktopInsPreqWPT failed.
Action ID: SWXDesktopInsWPTInstalledAction
Failed to get msi version for UpgradeCode [{00F50064-7000-11D3-8CFE-1050048383C9}].
Technical details:
The property is unrecognized
Error code: 1608
Invalid data in HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\E5A00A437891E38418011307471668D7
Action CheckInstalledMsiVersionAction from feature CODE\win_b64\SWXDesktopInsPreqVBA71 failed.
Action ID: SWXDesktopInsVBA71InstalledAction
I ended up searching for those hashes in the registry, “BE85C2B02A76B522062B1D99E055DD33“, and “E5A00A437891E38418011307471668D7“. Then deleting registry keys where a sub part mentioned Dassault Systems. After that I could progress with the install. Again, this seems to happen if you had Solidworks 2020 installed at any point.